Mobile Device Security Options
 Enterprises have to have ways to protect that data regardless of its location or place of breach. Options available to the enterprise include:
Enterprises have to have ways to protect that data regardless of its location or place of breach. Options available to the enterprise include:
- VPN - Many enterprises use Internet Protocol Security (IPSec) VPNs, but the fact that IPSec works at the network layer can add exposure of the entire network to malware found on remote machines.
- Network Access Control (NAC) - NAC gives the network the ability to grant access to a device based on preset criteria, and then monitor it throughout its connection cycle.
- Encryption - A data-level form of protection, encryption is centrally managed and updated.
- Intrusion detection and prevention - Intrusion detection and prevention systems focus on identifying incidents, logging information about them, taking action to stop intrusions and reporting incidents to administrators for further review.
- Remote Lock Down and Data Destruction - Credentials and devices that are tagged as inactive can have "self destruct" or "remote lock down" code downloaded and activated in such a way that all of the "sensitive data" on the remote device is "erased" and the device put in such a state that it is not usable with intervention by the enterprise.
- Data leakage protection - You can secure data, regardless of where it is in relation to the network, with data leakage prevention (DLP) technology. DLP solutions tag data based on a set of criteria such as location of data, application type, file type, keywords and common data strings.
Read on Order Mobile Device Policy Download Selected Pages
Janco Documents Why Recovery Plans Fail
Businesses that do not have business continuity plans that work run the risk of not being able to re-open their doors
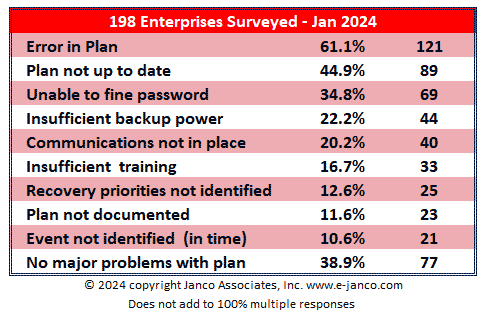
Many disaster recovery (DR) plans end up being a documentation exercise and never rise above the day-to-day priorities of the business. Those that make it to the DR testing phases often encounter problems that if not properly addressed leave a bad mark on the whole DR processes. In a survey of 253 enterprises that had to activate their recovery plans Janco has identified the reasons why recovery is not successful.
Steps to Take Before a Disaster Strikes
 The news is full of disasters and it is clear that they will continue to occur, be they tornadoes, hurricanes, fires, floods, or earthquakes. The risk that many enterprises face is that they are not ready with complete Business Continuity and Disaster Recovery Plans.
The news is full of disasters and it is clear that they will continue to occur, be they tornadoes, hurricanes, fires, floods, or earthquakes. The risk that many enterprises face is that they are not ready with complete Business Continuity and Disaster Recovery Plans.
Janco and the IT Productivity Center have developed a short list of things that enterprises of all sizes can implemented with little cost that could mitigate extensive losses and provide for safety of it employees. Those steps are:
- Validate that police and other first responders can contact the right people in your business - Research the Reverse 911 program for your area and register your business cell phones, voice over IP numbers or pagers. In an
emergency situation, Reverse 911 enables emergency officials to send out an
automated call to everyone registered in a specific area with important
information. - Program emergency numbers into business cell phones - Save emergency phone numbers for local police and fire departments into your cell phones.
- Create a business phone tree - Each enterprise facility should have a plan for contacting employees during emergencies through a designated phone tree. Designated staff should have copies of the phone tree and be trained on who they should call. Management should review and update the phone tree quarterly and conduct regular training sessions. Management should also have back-up copies of employee business mobile and personal phone numbers and their emergency contacts. This information should be regularly updated.
- Register your employee's business cell phone number - Individual employees should make sure family; friends and co-workers have their business mobile or BlackBerry numbers. Each person's business cell phone number should registered with a company like WhitePages.com. This will give colleagues and family members the ability to quickly find the information should they not have it on hand.
- Enable texting on Mobile Devices - Sometimes cell phone signals can become congested during emergencies, and it can be difficult to make or receive calls. Short text messages might be easier to get through.
Plus, texting helps to conserve battery power. -
 Have emergency back-pack kits accessible - Companies should organize and maintain emergency back-pack kits in several places. There should be designated staff responsible for grabbing these in the event of an emergency. Make sure it contains a company phone tree, key contact phone numbers, minimum of provisions for at least three days. Include fresh water, non-perishable food, a manual can opener, blankets, extra clothing, a first-aid kit, matches, a flashlight, a battery-operated radio and extra batteries. Test or replace the batteries at least once a year, especially for smoke alarms.
Have emergency back-pack kits accessible - Companies should organize and maintain emergency back-pack kits in several places. There should be designated staff responsible for grabbing these in the event of an emergency. Make sure it contains a company phone tree, key contact phone numbers, minimum of provisions for at least three days. Include fresh water, non-perishable food, a manual can opener, blankets, extra clothing, a first-aid kit, matches, a flashlight, a battery-operated radio and extra batteries. Test or replace the batteries at least once a year, especially for smoke alarms. - Create back-up copies of documents, data files, and software - At a secondary location, keep back-up copies of your important enterprise records and financial statements. Be sure to store important original paperwork in a safe and secure location. This way, you can grab it all quickly in the event of an emergency.
- Have cash available - Set aside an emergency fund of cash or traveler's checks or both. Keep them in a safe, accessible spot in case of the need for
evacuation. Banks and ATMs are often inaccessible during catastrophes. - After the disaster have employees register with the American Red Cross - Register with the Red Cross's Safe and Well Web site. If you have been affected by a disaster, this Web site provides a way for you to register yourself as "safe and well."