Data Breach Sources and Associated Losses Identified in Survey
Business must be proactive in guarding against data breaches and security intrusions
Data breaches are a fact of life with the advance of WiFi, 3G, and remote computing as it is done in today's flexible business environment. In a recent survey of companies that experienced data breaches Janco found that most are done by individuals
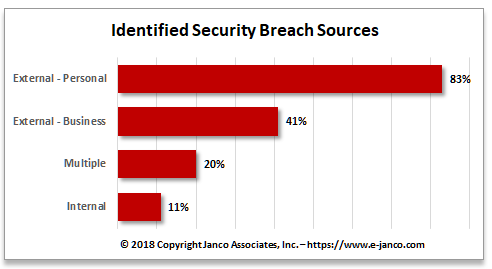
Most data breaches are caused by external sources. Breaches attributed to insiders, though fewer in number, are typically much larger than those caused by outsiders when they did occur. As a reminder of risks inherent to the extended enterprise, business partners and customers are behind well over a third of all data breaches. There are many instances where there is a collusion of internal and external sources to breach enterprise data - These typically are the most expensive and difficult to prevent and detect.
Data breaches and network intrusions occur because the personal information compromised includes data elements useful to phishing attackers and identity thieves, such as Social Security numbers, account numbers, and driver's license numbers. Some breaches do not expose such sensitive information; however, they still expose individuals to identity theft and business to a compromise of their electronic assets and that must be disclosed under Sarbanes-Oxley and various state laws.
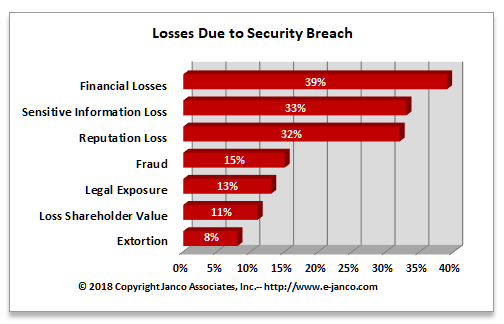
Cost of Data Breaches
Financial losses due to a data breach or a security breach average over $1.5 million USD.
Janco has defined a set of tools which enterprises of all sizes can use to be prepared to protect against breaches and intrusion, know when it occurs, and provides the ability to respond quickly when it does happen.
Key to protection is a definition and implementation of security policies and procedures which meet all of the compliance requirements placed on enterprise. Once that is accomplished, a strict audit regiment needs to be implemented.
The Data Breach and Network Intrusion Detection Tools are the tools that are needed:
- Security Manual Template
- Security Audit Program