Best Practices for Chief Information Officer - CIO
The Best Practices news feed is an XML news feed that you can subscribe to and re-publish on your web site or blog. The only requirement that you need to meet is that the feed is included with no modifications and that the links within the feed are retained as is.
If you wish to subscribe to this news feed the option that you have is:
IT Job Families Define Structure of IT Teams
CIO Resource Site News Feed
System Analyst Job Classes defined - Added to IT Professional Job Family
A modern IT structure includes team members who are representative of customers or the people engaging customers. For example, a consumer banking IT team should include a teller or bank manager, she contends, and a retail enterprise should enlist a store manager as part of an IT delivery team. Being a business leader means understanding the customer, and you can't do that if all you're doing is wearing an IT hat. You have to create a team that includes some unconventional players.
The first step is have a structure which provides a framework that is easy to implement. For example, one job family defined in the IT Job Family Classification and Pay Grade System, the IT System Technology Professional Family. With that in place the creation of pay grades to include the System Analyst Class is straight forward.
Read On Order Classification Pay Grade System Download Sample
Chief AI Officer and Project Manager AI added to IT Salary Survey Data
High demand for AI/ML IT Professionals drives salaries up
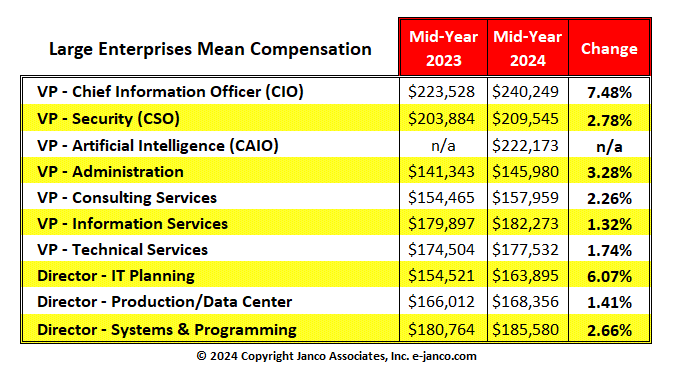
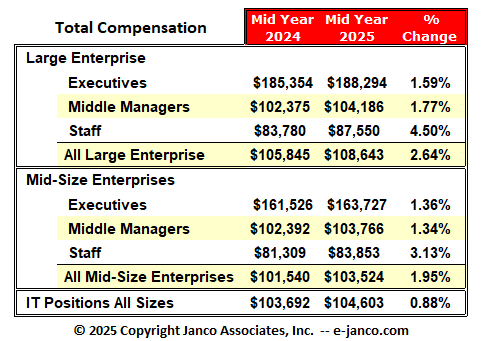
High demand for IT Pros with Artificial Intelligence and Machine Learning skills and inflation are driving up salaries. Median salaries for the positions surveyed now is $103,692. The data now includes compensation for Chief Artificial Intelligence Officer and Project Manager Artificial intelligence.
IT Job Descriptions - 2024 Edition Released
334 Job Descriptions included in the latest Edition of theInternet and Information Technology Positions Description HandiGuide
The 334 positions include all of the functions within the IT group. The Job Descriptions have been updated to be compliant with PCI-DSS, GDPR, Sarbanes-Oxley, HIPAA, CobiT, and the ITIL standards. The job descriptions are all structured to focus on "Best Practices" as defined by the IT Productivity Center to meet the requirements of World Class Enterprises. They are ready to use and easily modified to meet your enterprise's unique requirements.
Each job description is between two (2) to six (6) pages in length and has been created utilizing CSS style sheets. As such they are "out of the box" ready to use with little or no modification other than organization specific customization.
334 Internet and IT Job Descriptions as individual files in MS WORD and ePub formats. Long file names have been used to make customization easier.
Order IT Job Description HandiGuide Sample Description Download TOC
Technology Resilience and Business Continuity
Technology resilience - DRP and BCP
Technology resilience is defined as an organization's ability to maintain acceptable service levels through, and beyond, severe disruptions to its critical processes and the IT systems which support them.
Seven (7) factors C-level executives can use to get a clear grasp of what their enterprise's technology resilience is.
- Awareness is having the knowledge of what are the normal business operation requirements are; what dependencies there are on
- Protection is more than having physical and system access and security controls.
- Discovery is to know when a failure occurs.
- Preparedness means having specific action steps and plans in place to address the effects of a disruption.
- Recovery focuses on returning services and operations to business as usual levels within defined timescales and with minimal acceptable data loss following an event causing disruption or failure.
- Review and Assessment is essential for every technology resilience program, and includes post-incident reviews to identify the root causes of disruptions.
- Improvement is the process of taking the knowledge gained from all the above and taking steps to improve systems and increase resilience, and to continuously refine disaster recovery and business continuity plans.
Supply Chain Cyber Attacks on the rise
Managing a Supply Chain Security Management System (SCSMS)
A hot topic is the impact of Software supply chain (SSC) attacks with data showing these attacks rising more than 742% over the past three years.
With such continued growth, organizations continue to look for ways to mitigate the risks of SSC attacks, and various industry organizations continue to publish guidance to help organizations. The latest release comes from the US National Institute of Standards and Technology (NIST), in its special publication 800-204, also known as Strategies for the Integration of Software Supply Chain Security in DevSecOps CI/CD Pipelines.
Order Supply Chain Audit Program Download sample
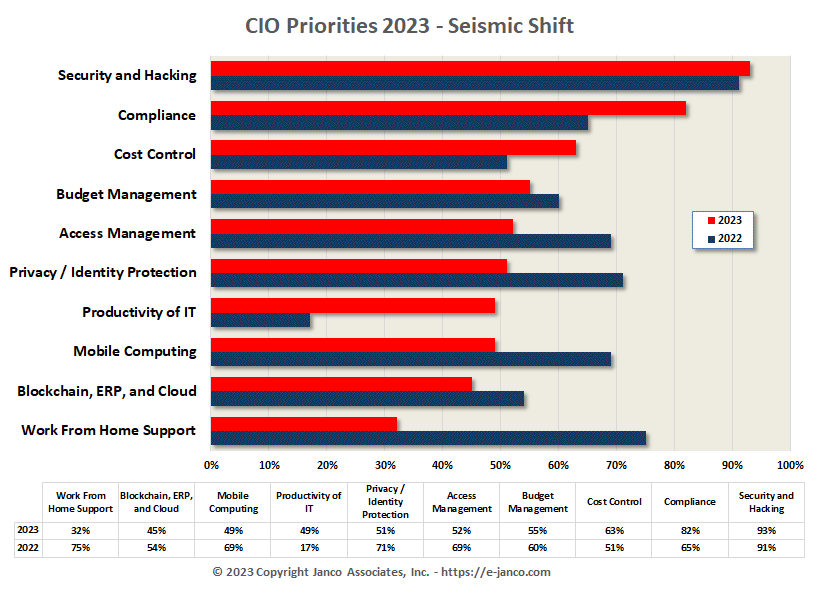
CIO Planning Priorities
Top CIO Management and Planning Priorities
Janco conducted a survey of 274 IT functions across multiple industries and from mega corporations to companies with as few as 50 IT professionals. In 2023 the top 10 priorities:
Download TOC IT Mgt Tool Kit Order IT Management Tool Kit
Top 10 Social Network Security Tips
Top 10 Social Networking Tips
Top 10 tips to improve social networking securitySocial Networking Policy
- Educate employees
- Have employees use different passwords for different system
- Mandate strong passwords
- Have employees change passwords regularly
- Do not share accounts
- Implement two factor authentication
- Educate employees to NOT open email attachments or go to links where the originator is not known
- Utilize antivirus and security software
- Don't friend people you do not know
- Validate and verify
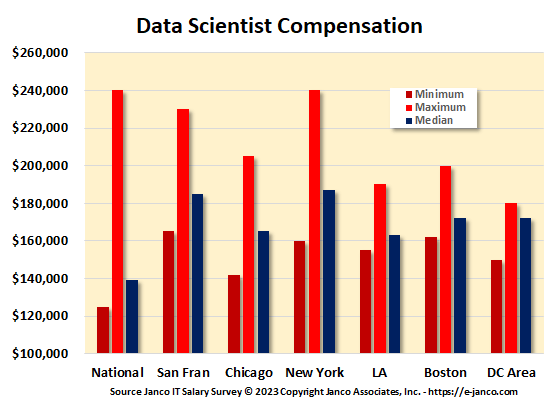
Data Scientist Job Description and Salary Data
Data Scientist Job Description
Order Data Scientist Job Description
Data Scientist Job Description - Hot New Job Title - In a recent article in the Harvard Business Review, the sexiest job of the 21st Century is that of Data Scientist. The job description created Janco has provides a clear definition of that role the individual plays in an organization.