IT Related Fraud is More Prevalent
CIOs need to be aware of fraud that can occur on their systems
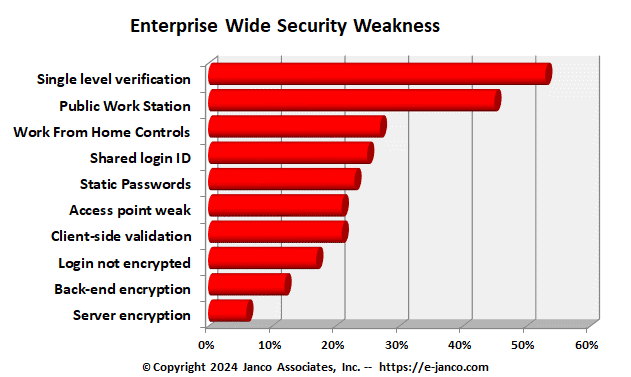
IT Related Fraud is More Prevalent - Security is more than compliance to mandated requirements. CIOs not only need to be concerned with protection of sensitive information but the specter of fraud and theft is a pressing concern. With the greater dependence by corporation on open Internet based systems there has been a notable increase in fraud and theft.
Janco in its monthly interviews of CIOs found that one in five organizations has experienced some type of fraud associated with their systems.
The results of this analysis agree with a report that was recently published in the CFO magazine. They report that Seventy percent of survey respondents polled said their companies experienced fraud in the previous 12 months, compared to 61 percent for the prior 12-month period, which surveyed 901 senior executives, 53 percent of them at the C-suite level. The fraud they found went beyond IT systems.
Data Security and Protection are a priority and this template is a must have tool for every CIO and IT department. Over 3,000 enterprise worldwide have acquired this tool and it is viewed by many as the Industry Standard for Security Management and Security Compliance.
Read on CIO Job Description Order CIO Job Description
Security Manual Template purchase options
Order Security Manual Template Multi-Country License Download sample